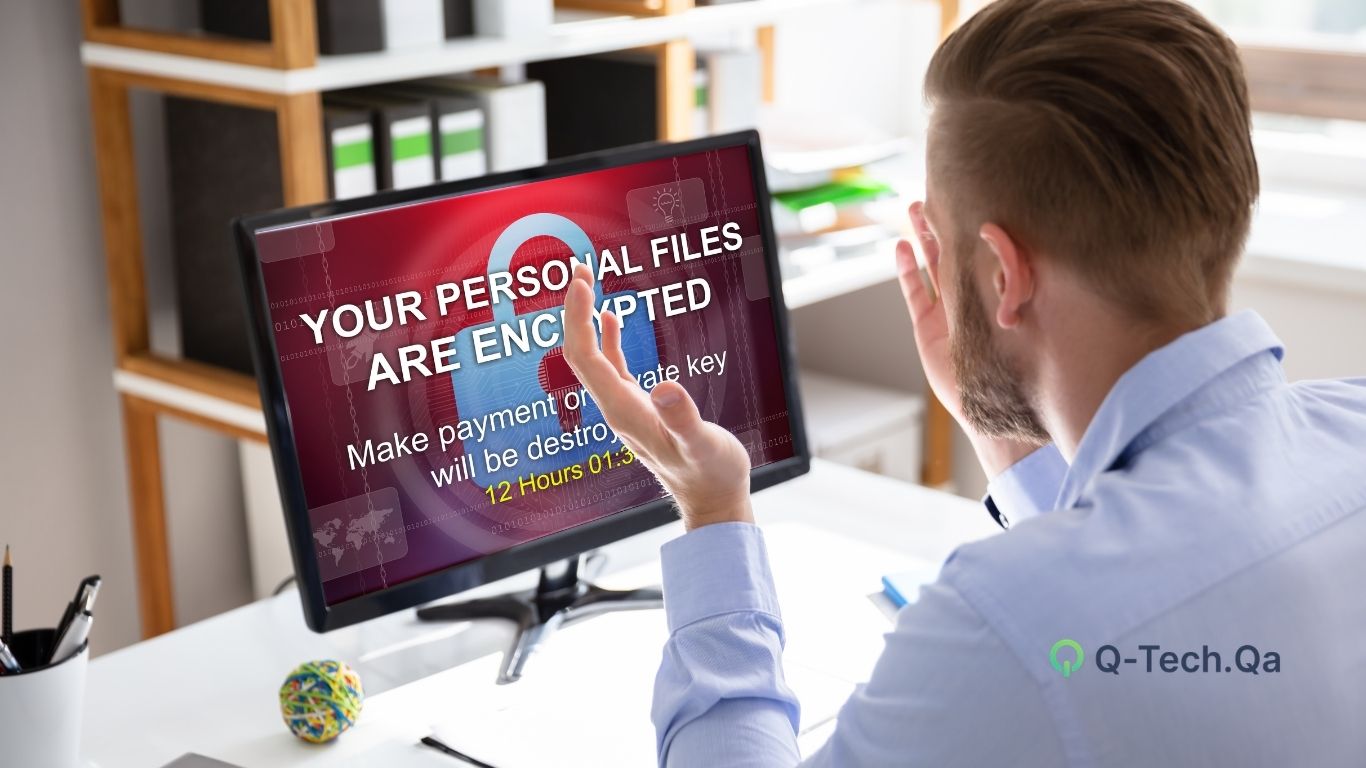
In today’s always-on digital environment, even a few minutes of downtime can result in significant financial loss, reputational damage, and operational disruption. Whether it’s a cyber attack, hardware failure, natural disaster, or human error, unexpected incidents can bring business operations to a halt.
That’s where Disaster Recovery (DR) and Business Continuity (BC) solutions become essential. Our comprehensive DR & BC services ensure that your critical systems, applications, and data are protected and can be quickly restored—keeping your business running smoothly under any circumstances.
What is Disaster Recovery & Business Continuity?
Disaster Recovery (DR) and Business Continuity (BC) are strategic approaches designed to ensure that organizations can continue operating during and after a disruption.
- Disaster Recovery focuses on restoring IT systems, applications, and data after an incident.
- Business Continuity ensures that essential business functions continue without interruption.
Together, they form a complete resilience strategy that protects your organization from both short-term disruptions and long-term operational risks.
Modern DR & BC solutions leverage cloud technologies, automated backups, and rapid failover mechanisms to ensure minimal downtime and fast recovery.
We provide end-to-end Disaster Recovery and Business Continuity services tailored to your business needs.
Common Challenges We Solve
Many organizations underestimate the risks associated with downtime and data loss. Our solutions address key challenges such as:
- Unexpected system failures and outages
- Increasing cyber threats like ransomware
- Data loss due to human error or hardware issues
- Lack of a structured recovery plan
- Compliance and regulatory requirements
- High cost of downtime and operational disruption
Without a proper DR & BC strategy, businesses risk losing critical data and customer trust.



