Clients Secured
Assessments Done
Vulnerabilities Found
Countries Served
Why Network Security Assessment Matters
Every organization faces these critical risks. Without proper assessment, these vulnerabilities become attack vectors for adversaries.
Firewall & IDS/IPS Bypass Techniques
Testing firewall rule effectiveness, evasion techniques, protocol tunneling, and fragmentation attacks to validate your perimeter defenses against sophisticated adversaries.
Network Segmentation Failures
VLAN hopping, inter-zone traversal, and microsegmentation bypass. We validate that network boundaries actually prevent lateral movement between security zones.
Wireless Network Exploitation
WPA2/WPA3 attacks, rogue access points, evil twin attacks, and wireless client isolation testing for enterprise Wi-Fi infrastructure.
Active Directory Compromise
Kerberoasting, AS-REP roasting, Pass-the-Hash, Golden/Silver Ticket attacks, and DCSync exploitation - testing the crown jewels of enterprise identity infrastructure.
Man-in-the-Middle Attacks
ARP spoofing, LLMNR/NBT-NS poisoning, DNS hijacking, and WPAD exploitation enabling credential harvesting and traffic interception on internal networks.
Legacy Protocol Vulnerabilities
Telnet, FTP, SMBv1, NTLMv1, and other legacy protocols creating authentication bypass and data interception opportunities across your network.
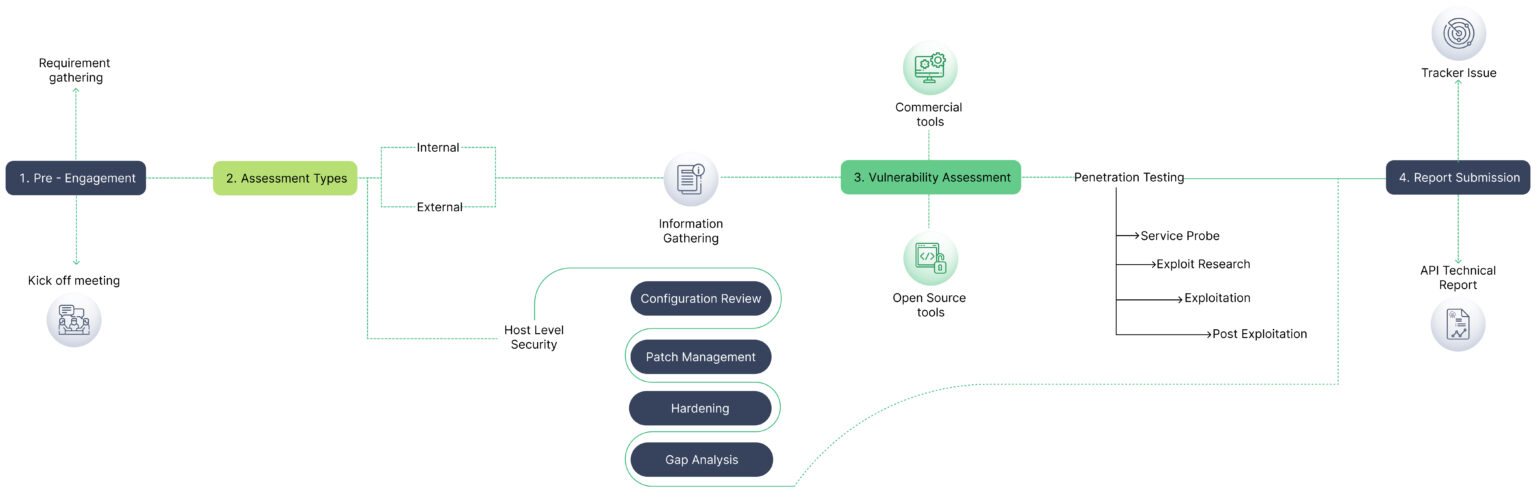
Assessment Process
A structured, repeatable methodology delivering consistent, high-quality results across every engagement.
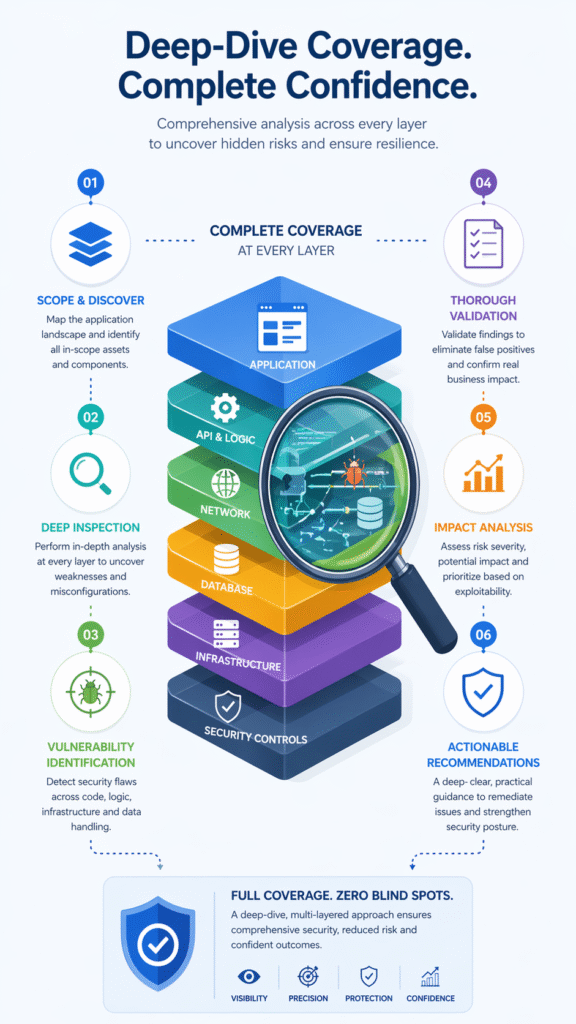
Deep-Dive Coverage - Every Nuance Addressed
Network Security Assessment isn't one-size-fits-all. Different contexts demand different assessment approaches. We go beyond generic checklists to address the specific attack surfaces and risks of each domain.
External Attack Surface Enumeration & Exploitation
A mature network assessment validates what an adversary can really reach from the internet, not just what asset inventories claim exists. The work emphasizes exposed appliances, weak protocols, and management planes that collapse perimeter assumptions
Active Directory & Hybrid Identity Attack Paths
Enterprise network compromise is usually decided by identity architecture, especially where on-premises Active Directory and cloud identity coexist. This domain maps how misconfigurations in Kerberos, PKI, delegation, and synchronization create enterprise-wide blast radius.
Segmentation & East-West Control Validation
Networks often look segmented on diagrams while still permitting broad adversary movement in practice. Testing validates whether VLANs, ACLs, NAC, and routing boundaries actually prevent traversal between business-critical tiers.
Resilience Against Adversary Tradecraft
The objective is not just to find exposed services but to validate how the network withstands realistic post-compromise behavior. This domain measures whether detection and preventive controls meaningfully constrain modern attacker tradecraft.
Learn More About cloud security assessment
Watch our expert walkthrough and grab the detailed flyer to easily share with your team and stakeholders.
What clients say about our Managed IT Services


FAQ
How long does the Network Security Assessment take?
Typically 1-3 weeks depending on scope and complexity. We provide a detailed timeline during the scoping phase based on your specific environment and requirements
Will the assessment affect our production systems?
We use carefully controlled, non-destructive testing techniques for production environments. For invasive tests, we coordinate timing with your team and can test on staging environments.
What certifications do your testers hold?
Our team holds OSCP, CREST CRT, CEH, CISSP, and CISM certifications. Briskinfosec is CREST-approved for both Vulnerability Assessment and Penetration Testing – the only Indian company with this dual accreditation.
Do you provide re-testing after remediation?
Yes. We include one round of complimentary re-testing within 90 days to validate all findings have been properly remediated. The re-test report is provided through our LURA portal.
What deliverables do we receive?
You receive a comprehensive report with executive summary, detailed technical findings with CVSS scores, proof-of-concept demonstrations, risk-prioritized remediation guidance, and access to our LURA portal for ongoing tracking.
