smartphone users globally — mobile apps are the world's most used attack surface
of mobile apps fail basic security tests on first assessment
mobile application assessments completed across Qatar & GCC
free remediation retest included on every mobile app engagement
Why mobile application security testing matters
Your mobile app sits on millions of devices — storing sensitive data, accessing backend APIs, and handling financial transactions. Without rigorous security testing, it becomes your weakest link and your users’ greatest risk.
Mobile apps store highly sensitive data locally
Banking credentials, health records, location data, authentication tokens, and personal information are routinely stored insecurely on device storage. Unencrypted SQLite databases, plaintext SharedPreferences, and exposed Keychain entries are among the most common — and most damaging — vulnerabilities our testers find.
Mobile APIs are a direct path to your backend
Every mobile app communicates with backend APIs — and those APIs are often less rigorously secured than web-facing endpoints. Insecure direct object references, missing authentication on internal API calls, and unencrypted traffic in development builds are routinely exploitable via mobile app testing.
Reverse engineering exposes your business logic
Without proper code obfuscation, binary protection, and tamper detection, attackers can decompile your mobile app to extract API keys, hardcoded credentials, proprietary algorithms, and server endpoints — turning your app into a roadmap for attacking your backend infrastructure.
App store rejection and removal risk
Both Apple App Store and Google Play Store actively scan for insecure coding practices, privacy violations, and dangerous permissions misuse. An insecure app can be rejected pre-launch or removed post-launch — causing revenue loss, brand damage, and user distrust that is extremely difficult to recover from.
What our mobile app security assessment covers
Our assessment covers both iOS and Android platforms — combining static analysis, dynamic runtime testing, network traffic interception, and manual expert review aligned to the OWASP Mobile Application Security Verification Standard (MASVS).
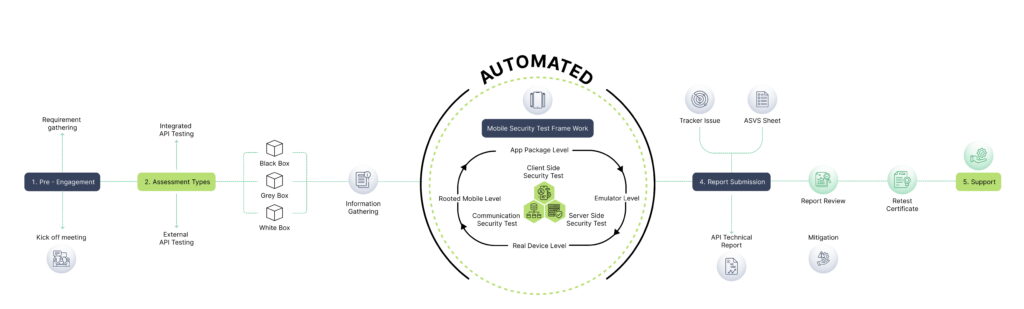
Our mobile security testing methodology
Our mobile app security testing methodology
Scoping & environment setup
We begin with a detailed scoping session to define the platforms in scope (iOS, Android, or both), the testing environment (production, staging, or test build), testing type (black-box with compiled binary only, or grey/white-box with source code access), and any functionality requiring special handling — such as payment flows, biometric authentication, or third-party SDK integrations. We provide a pre-engagement checklist to ensure the right builds, test accounts, and API environments are ready before testing begins.
Dynamic runtime testing
The application is installed on real devices and emulators and subjected to comprehensive runtime testing — using Frida for dynamic instrumentation to hook into application functions, bypass security controls, and monitor runtime behaviour. We analyse memory contents, file system activity, and inter-process communication during active use to identify data leakage, insecure logging, and runtime security control weaknesses that are invisible in static analysis.

Static analysis & binary review
The application binary is decompiled and subjected to thorough static analysis — reviewing the code for hardcoded secrets (API keys, credentials, tokens), insecure cryptography implementation, dangerous permissions declarations, third-party library vulnerabilities, improper data handling patterns, and binary protection mechanisms. For iOS we analyse the IPA using class-dump and Hopper; for Android we use jadx, apktool, and MobSF to reconstruct readable source code from the APK or AAB.
Network traffic & API testing
All network communications between the mobile app and its backend APIs are intercepted using Burp Suite and Proxyman — with SSL pinning bypassed where implemented — to analyse the security of data in transit, identify insecure endpoints, test API authentication and authorisation controls, and verify that sensitive data is never transmitted unencrypted. API endpoints discovered through the mobile app are tested against the OWASP API Security Top 10 for comprehensive backend coverage.
Learn More About mobile security testing
Watch our expert walkthrough and grab the detailed flyer to easily share with your team and stakeholders.
What you receive
Every mobile application security engagement includes a complete assessment and reporting package — designed for development teams, business leadership, app store submissions, and regulatory compliance.
Executive summary report
Plain-English risk overview for leadership and non-technical stakeholders — with clear business impact framing and overall security posture rating.
Detailed technical findings report
Full vulnerability descriptions, reproduction steps, proof-of-concept screenshots, and platform-specific iOS and Android remediation guidance for developers.
CVSS-scored vulnerability register
Every finding rated Critical, High, Medium, Low, and Informational — with CVSS v3.1 scores and OWASP MASVS category mapping for each issue.
OWASP MASVS compliance mapping
Findings mapped to MASVS-L1 and MASVS-L2 controls, OWASP Mobile Top 10, PCI-DSS, ISO 27001, and Qatar Data Protection Law requirements.
Free remediation retest report
A follow-up assessment against your updated app build confirming all vulnerabilities have been fully resolved — included at no extra charge on every engagement.
Proof-of-concept evidence
Annotated screenshots, Frida scripts, network traffic captures, and exploit demonstrations confirming every vulnerability finding with irrefutable evidence.
Who we help
Our mobile application security testing serves organisations across Qatar and the GCC — from fintech startups launching their first app to banks securing millions of daily mobile banking transactions.
Mobile banking & payment apps
Security assessment of internet banking apps, digital wallet platforms, and payment applications — ensuring PCI-DSS compliance and QCB regulatory requirements are met for Qatar's mobile financial services.
Government e-service mobile apps
Security testing of citizen-facing government mobile applications — Metrash2, Hukoomi, and public-sector apps — aligned to Qatar's QNCSF and ictQATAR mobile security guidelines.
Health & patient mobile platforms
MASVS-aligned assessment of mHealth applications, telemedicine platforms, and hospital patient apps — protecting sensitive health data and ensuring Qatar Data Protection Law compliance.
Shopping & loyalty apps
Security testing for retail mobile apps, loyalty platforms, and in-app payment flows — protecting customer payment data and ensuring PCI-DSS compliance for Qatar's growing mobile commerce sector.
SaaS & enterprise mobile apps
Pre-launch and ongoing security assessment for enterprise mobile applications and B2B SaaS platforms — providing security assurance for client due diligence and app store submission requirements.
Booking, travel & logistics apps
Mobile security testing for hotel booking apps, travel platforms, ride-hailing services, and logistics applications — protecting user data and payment information across Qatar's hospitality and transport sector.
What clients say about our Managed IT Services


FAQ
What is mobile application security testing?
Mobile application security testing is a structured assessment of your iOS or Android application — combining static code analysis (examining the app binary without running it), dynamic runtime testing (analysing the app while it is running on a real device), network traffic analysis (intercepting communications between the app and its backend), and manual expert review to identify security vulnerabilities. The goal is to find weaknesses that could allow attackers to steal user data, bypass authentication, reverse engineer your proprietary code, or compromise your backend infrastructure — before your users or attackers discover them first.
What is the OWASP MASVS and why does it matter?
The OWASP Mobile Application Security Verification Standard (MASVS) is the globally recognised framework for mobile application security — defining the security requirements that mobile apps should meet at two levels: MASVS-L1 (standard security — the baseline every app should achieve) and MASVS-L2 (defence-in-depth — for apps handling highly sensitive data like banking, healthcare, or government services). It matters because it is referenced by PCI-DSS, ISO 27001, and Qatar’s regulatory frameworks as the benchmark for mobile security assessment. Every one of our assessments is aligned to MASVS and the accompanying OWASP Mobile Application Security Testing Guide (MASTG).
When should we commission a mobile app security assessment?
You should commission a mobile security assessment: before your first public app store release — to ensure you do not launch with exploitable vulnerabilities; after significant feature releases — new features introduce new attack surface; annually as part of your security programme — the threat landscape evolves continuously; when required for compliance — PCI-DSS, QCB, and ISO 27001 all have mobile security requirements; and when required for client or partner due diligence — enterprise clients increasingly require security assurance before deploying staff-facing mobile apps. Earlier is always better — finding vulnerabilities in development is far cheaper than fixing them post-launch.
Do you test both iOS and Android, and are they assessed separately?
Yes — we test both iOS (IPA files, App Store and TestFlight builds) and Android (APK and AAB files, Play Store and enterprise builds). They are assessed as separate platforms because they have distinct security architectures, data storage mechanisms, permission models, and vulnerability patterns. iOS testing uses tools such as Objection, Hopper, and Frida on jailbroken devices, while Android testing uses jadx, apktool, MobSF, and Frida on rooted devices. We recommend testing both platforms if your app has both an iOS and Android version — the same backend API vulnerabilities may manifest differently on each platform.
Can you test a mobile app that is not yet published on the App Store or Play Store?
Yes — and pre-launch testing is actually the most valuable time to conduct a mobile security assessment. You can provide us with your app build directly (IPA for iOS, APK or AAB for Android) without it needing to be available on any public app store. Testing pre-launch means vulnerabilities can be fixed before users are exposed, before the app undergoes App Store security reviews that could flag issues, and before any breach could affect real user data. We strongly recommend commissioning a security assessment as part of your pre-launch readiness checklist for any app handling sensitive data or financial transactions.
How long does a mobile app security assessment take?
Duration depends on the size, complexity, and number of platforms being tested. A straightforward single-platform app (iOS or Android only) with standard functionality typically takes 4–7 business days of testing. A medium-complexity app with authenticated areas, in-app purchases, biometric authentication, and API coverage typically takes 7–12 business days. A complex enterprise app or combined iOS and Android assessment with extensive backend API coverage may take 2–4 weeks. We provide a detailed timeline estimate during scoping — including testing days, analysis time, and report delivery date — before any work begins.
What do we need to provide before the assessment can begin?
To start the assessment efficiently, we typically require: the app build file (IPA for iOS, APK or AAB for Android) or TestFlight/internal testing track access; test account credentials for each user role available in the app; backend API base URL and any API documentation (for grey/white-box testing); details of any third-party integrations or payment gateways; source code access if white-box testing is agreed; and contact details for a technical team member available during testing to answer questions. We provide a structured pre-engagement checklist during scoping to guide your preparation — most teams can complete this within a few days.
How does the remediation retest work for mobile apps?
After your development team has applied fixes, you provide us with an updated app build (new IPA or APK). Our testers retest every identified vulnerability against the updated build — actively re-attempting each exploit technique to confirm the fix is effective, not just reviewing a developer’s confirmation. We test each fix in context — for example, verifying that a data encryption fix actually encrypts data at rest correctly, not just that the relevant code was updated. Any vulnerabilities not fully resolved are documented with updated status. The retest results in a formal retest report and letter of attestation confirming remediation is complete.
