of cloud security incidents are caused by misconfiguration — not external hacking
cloud security assessments completed across Qatar, GCC & wider Middle East
faster cloud adoption in Qatar since 2021 — dramatically expanding the cloud attack surface
of assessments include a remediation retest and formal letter of attestation
Why cloud security assessment matters
Qatar’s organisations are migrating to the cloud at speed — but the shared responsibility model means cloud providers only secure the infrastructure, not how you configure and use it. That configuration gap is where the vast majority of cloud breaches begin.
Misconfiguration is the leading cause of cloud breaches
Overly permissive IAM policies, publicly exposed S3 buckets, unencrypted storage volumes, unrestricted security groups, and disabled audit logging are the most common — and most exploited — cloud vulnerabilities. These are not sophisticated attacks. They are configuration errors that anyone with access to the internet can exploit.
Cloud identity and access management is critically over-privileged
Excessive IAM permissions — developer accounts with production access, service accounts with administrator roles, and overly broad permission policies — are endemic in cloud environments. A single compromised credential with excessive permissions can expose an entire cloud estate within minutes.
The shared responsibility model is widely misunderstood
AWS, Azure, and GCP secure the underlying infrastructure — but everything you build on top of it is your responsibility. Data classification, access controls, encryption, monitoring, and network configuration are all customer responsibilities. Many Qatar organisations discover this only after an incident.
Cloud environments drift continuously from secure baselines
Cloud infrastructure changes daily — new services are deployed, configurations are modified, permissions are granted, and integrations are added. Without continuous assessment, secure cloud environments drift into insecure states faster than point-in-time assessments can track. What was secure last quarter may not be secure today.
What our cloud security assessment covers
Our assessment goes far beyond automated scanning — combining CIS Benchmark reviews, IAM privilege analysis, network architecture assessment, data security review, and workload security testing across your entire cloud estate.
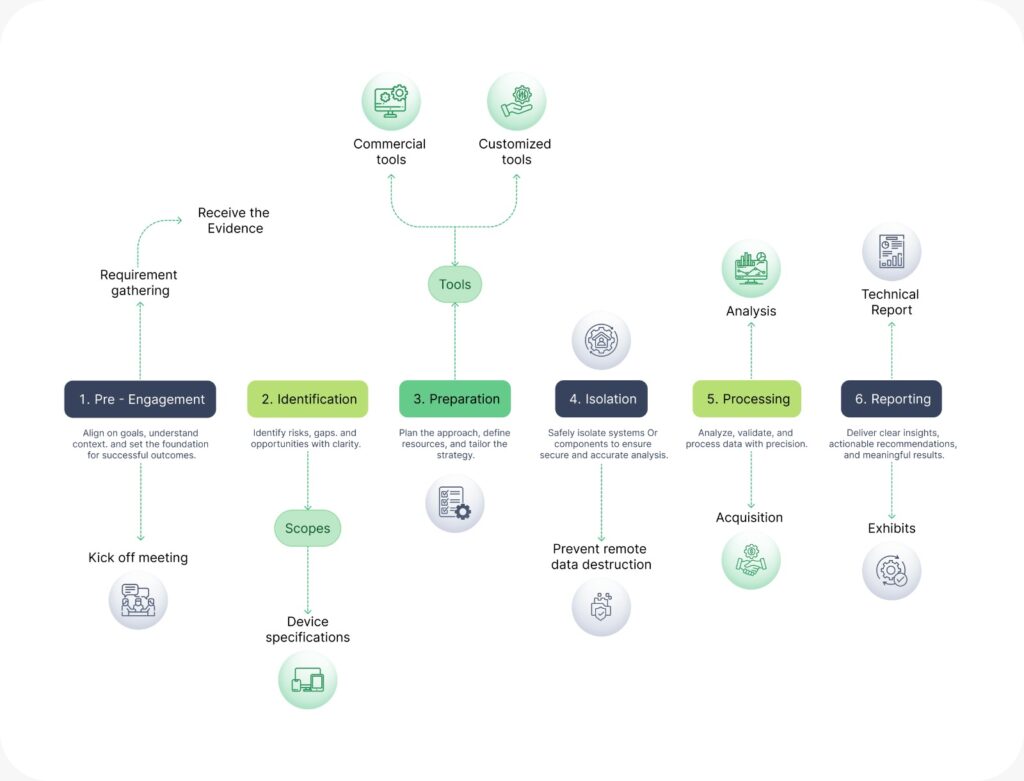
Our cloud security assessment methodology
Our cloud security assessment methodology
Scoping & access provisioning
We begin with a detailed scoping session to define the cloud platforms in scope (AWS, Azure, GCP, or multi-cloud), the accounts and subscriptions to assess, the assessment type (read-only security review, active penetration testing, or compliance gap assessment), and any workloads requiring special handling. We then work with your team to provision read-only assessment access — using dedicated IAM roles or managed identity with the minimum permissions needed to conduct the assessment without modifying any resources.
IAM & privilege analysis
Our analysts perform deep manual review of the IAM configuration — examining every policy, role, user, and service account for violations of the principle of least privilege, privilege escalation paths, cross-account access risks, unused credentials, and missing MFA enforcement. This is the highest-impact phase of the assessment — IAM misconfigurations are the most common route to full cloud environment compromise and require expert human analysis to identify reliably beyond what automated tools detect.
Automated cloud security scanning
We run comprehensive automated scans across your cloud estate using industry-leading cloud security posture management (CSPM) tooling — including Prowler, ScoutSuite, Checkov, and platform-native tools (AWS Security Hub, Azure Defender for Cloud, GCP Security Command Center). This phase produces an initial inventory of all cloud resources and a preliminary list of misconfigurations, non-compliant controls, and publicly exposed resources across the entire account or subscription scope.
Reporting & risk rating
You receive a comprehensive dual-audience report — an executive summary for leadership with business risk framing and cloud security posture scorecard, and a detailed technical findings report for your cloud and DevOps teams with resource-level findings, configuration evidence, and specific remediation steps for each platform. Every finding is risk-rated and mapped to CIS Benchmark controls, the applicable compliance framework, and a prioritised remediation roadmap structured for sprint-based cloud remediation workflows.
Learn More About cloud security assessment
Watch our expert walkthrough and grab the detailed flyer to easily share with your team and stakeholders.
What you receive
Every cloud security assessment delivers a complete findings and reporting package — structured for cloud teams, security leadership, compliance auditors, and client due diligence requirements.
Executive summary & cloud security posture scorecard
Plain-English risk overview for leadership — with overall cloud security posture rating, top risk areas, and business impact framing per finding category.
Detailed technical findings report
Resource-level findings with configuration screenshots, evidence captures, risk context, and platform-specific remediation steps for AWS, Azure, or GCP.
Annotated evidence exhibits
Clearly labelled screenshots, file listings, communication extracts, and log excerpts supporting each finding.
Complete cloud resource inventory
A full inventory of all assessed cloud resources — services, accounts, storage, compute, identity, and networking — providing a definitive baseline of your cloud attack surface.
Risk-rated vulnerability & misconfiguration register
Every finding rated Critical, High, Medium, Low, and Informational — with CIS Benchmark control mapping and business-context risk rating for each issue.
Compliance gap report
Findings mapped to CIS Benchmarks, CSA CCM, ISO 27001, PCI-DSS, Qatar PDPL, QCB IT Risk Framework, and QNCSF — your cloud compliance evidence package.
Who we help
Our cloud security assessment services support organisations across Qatar and the GCC — from enterprises mid-migration to cloud-native startups and regulated institutions managing sensitive data in multi-cloud environments.
Financial services cloud security
Cloud security assessment for Qatar banks, insurers, and fintech companies operating under QCB IT Risk Framework — ensuring cloud environments meet regulatory requirements for financial data processing and storage.
Government cloud & e-services
Security assessment of government cloud deployments — Ministry-operated cloud environments, shared government cloud platforms, and digital services hosted on public cloud — aligned to QNCSF and ictQATAR cloud security directives.
Health data cloud platforms
Cloud security assessment for hospitals, health networks, and digital health platforms migrating patient data to cloud — ensuring Qatar Data Protection Law compliance and protecting highly sensitive health records from misconfiguration exposure.
Cloud-native & SaaS companies
Cloud security assessment for technology companies and SaaS providers built entirely on cloud infrastructure — providing security assurance for enterprise clients, investors, and ISO 27001 certification bodies.
Energy sector cloud migration
Cloud security for Qatar's oil, gas, and energy sector as OT and IT systems move to hybrid cloud environments — assessing cloud configurations protecting operational data, asset management systems, and industrial control integrations
Real estate & smart city cloud
Cloud security assessment for real estate, construction, and smart city operators using cloud platforms for BIM data, smart building management, and project collaboration — protecting proprietary data across complex multi-party cloud environments.
What clients say about our Managed IT Services


FAQ
What is digital forensics and investigation?
Digital forensics is the science of identifying, preserving, analysing, and presenting digital evidence from computers, mobile devices, networks, and cloud platforms. It is used in legal proceedings, HR investigations, regulatory compliance, and cyber incident response. The goal is always to recover accurate, admissible evidence while maintaining strict chain-of-custody integrity — so findings can be relied upon in court, tribunal, or internal proceedings.
What types of devices and systems can you investigate?
We investigate a wide range of digital sources including: computers (Windows, macOS, Linux), mobile devices (iOS and Android smartphones and tablets), cloud platforms (Microsoft 365, Google Workspace, AWS, Azure), email systems (Exchange, Outlook, Gmail), servers and network infrastructure, USB drives and external storage, CCTV and IoT devices, and messaging applications (WhatsApp, Telegram, Teams). If data exists digitally, we can investigate it.
How is digital forensics different from a standard IT investigation?
Standard IT troubleshooting is not forensically sound — it often modifies or destroys the very evidence you need. Digital forensics uses write-blocking hardware, forensic imaging tools, and cryptographic hashing to ensure evidence is acquired without alteration. Every action is documented in a formal chain-of-custody log. This evidential integrity is what makes forensic findings admissible in legal proceedings — something a standard IT investigation cannot provide.
How quickly can you respond to an urgent forensic investigation?
We offer 24/7 emergency response for urgent forensic matters. For critical incidents — active ransomware attacks, suspected ongoing data theft, or time-sensitive legal matters — our team can typically be deployed on-site in Qatar within a few hours of engagement. For non-urgent matters, we typically begin within one business day. Early engagement is always better — the sooner we are involved, the more evidence we can recover and preserve.
When should an organisation engage a digital forensics investigator?
You should engage a digital forensics investigator as soon as you suspect an incident — not after you have tried to investigate it yourself. Common triggers include: a suspected data breach or cyber attack, suspicion of employee misconduct or data theft, a fraud or financial irregularity, a legal dispute requiring digital evidence, or a regulatory investigation. Acting quickly is critical — digital evidence can be overwritten, corrupted, or lost within hours if not properly preserved.
Can you recover deleted files, messages, and emails?
In many cases, yes. When a file is deleted, the data is not immediately erased from storage — only the reference to it is removed. Using specialist forensic tools, we can often recover deleted files, emails, WhatsApp messages, browser history, and application data from computers, mobile devices, and cloud systems. The success of recovery depends on how long ago data was deleted, whether the storage has been overwritten, and the type of device. Acting quickly significantly increases recovery success rates.
What information do I need to provide at the start of an investigation?
To scope an investigation effectively, it helps to provide: a description of what happened or what you suspect, the types of devices or systems involved, the relevant timeframe, the legal or business context (e.g. HR dispute, cyber incident, fraud), and any applicable deadlines (court dates, regulatory reporting deadlines). You don’t need to have all the answers — our scoping consultation is designed to help you define the investigation objectives clearly before we begin.
How long does a digital forensics investigation take?
Timelines vary depending on the scope and complexity of the investigation. A focused single-device investigation (e.g., one laptop or mobile phone) typically takes 5–10 business days from evidence receipt to report delivery. A multi-device or enterprise-scale investigation involving cloud platforms, servers, and multiple devices may take 3–8 weeks. For urgent matters — active incidents, imminent legal deadlines — we offer expedited investigation services. We always provide a timeline estimate at the scoping stage before work begins.
