of all cyber attacks target the application layer, not the network
web application assessments completed across Qatar & GCC
critical & high vulnerabilities discovered and remediated
free remediation retest included on every engagement
Why web application security assessment matters
Your web application is your most exposed attack surface. Every login form, API endpoint, session token, and user input is a potential entry point for attackers — and without regular testing, vulnerabilities remain invisible until exploited.
Automated scanners alone are not enough
Automated tools find common, known vulnerabilities — but miss the business logic flaws, authentication bypass routes, and custom code weaknesses that attackers actively exploit. Expert-led manual testing is essential to close the gap between what scanners see and what attackers can actually do.
APIs are the new attack frontier
Modern web applications rely heavily on REST and GraphQL APIs — often deployed with insufficient authentication, rate limiting, or input validation. API vulnerabilities are now among the most exploited attack vectors globally, yet routinely overlooked in basic security assessments.
Regulatory compliance demands regular testing
PCI-DSS, ISO 27001, Qatar Data Protection Law, and QCB IT Risk Framework all require or strongly recommend regular web application penetration testing. An annual VAPT assessment provides the documented evidence auditors and regulators expect to see.
Business logic flaws cause the biggest breaches
Price manipulation, privilege escalation, account takeover, and workflow bypass are business logic vulnerabilities that no scanner can detect. They require human testers who understand how your application is intended to work — and how to abuse it.
What our web application VAPT covers
Our assessment goes far beyond automated scanning — combining OWASP Top 10 coverage with deep manual testing of business logic, authentication, session management, and API security.
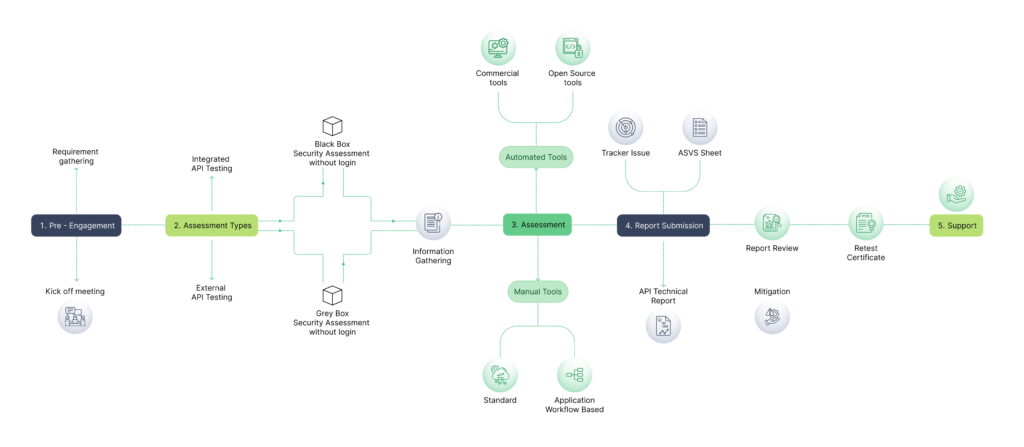
Our VAPT methodology
Our CREST-approved VAPT methodology
Scoping & planning
We begin with a detailed scoping session to define the assessment targets, testing type (black-box, grey-box, or white-box), rules of engagement, and any excluded functionality. We document authentication credentials, testing windows, and emergency contact procedures — ensuring testing is controlled, safe, and aligned to your operational requirements.
Vulnerability identification
We combine automated scanning with expert manual testing — using industry-standard tools alongside bespoke testing techniques to identify vulnerabilities across the full OWASP Top 10, business logic, authentication, session management, and API security categories. Every finding is manually verified to eliminate false positives before reporting.
Reconnaissance & mapping
Our testers perform both passive and active reconnaissance — mapping the application's attack surface, identifying all endpoints, parameters, authentication mechanisms, third-party integrations, and technology stack components. This phase builds the complete picture of what needs to be tested before any active exploitation begins.
Reporting & risk rating
You receive a comprehensive dual-audience report — an executive summary for leadership with business risk context, and a detailed technical report for your development team with step-by-step remediation guidance. Every finding is CVSS-scored and business-risk-rated, with a prioritised remediation roadmap that helps you fix the right things first. Reports are structured for use in compliance submissions, board presentations, and client due diligence.
Learn More About Web Application Security Assessment (VAPT)
Watch our expert walkthrough and grab the detailed flyer to easily share with your team and stakeholders.
What you receive
Every web application VAPT engagement includes a complete assessment and reporting package — designed for technical teams, business leadership, and regulatory submissions.
Executive summary report
Plain-English risk overview for leadership, board members, and non-technical stakeholders — with clear business impact framing.
Detailed technical findings report
Full vulnerability descriptions, reproduction steps, proof-of-concept screenshots, and technical remediation guidance for developers.
Annotated evidence exhibits
Clearly labelled screenshots, file listings, communication extracts, and log excerpts supporting each finding.
CVSS-scored vulnerability register
Every finding rated Critical, High, Medium, Low, and Informational — with CVSS v3.1 scores and business-context risk ratings.
Prioritised remediation roadmap
A fix-first action plan prioritised by business impact — telling your team exactly what to fix, in what order, with how-to guidance.
Compliance mapping
Findings mapped to OWASP Top 10, PCI-DSS, ISO 27001, Qatar Data Protection Law, and QCB IT Risk Framework requirements.
Who we help
Our web application VAPT services are used by organisations across Qatar and the GCC — from regulated financial institutions to fast-growing e-commerce platforms and government digital services.
Banks, fintech & payment platforms
Annual PCI-DSS and QCB-mandated web application testing for internet banking portals, payment gateways, and customer-facing financial platforms handling sensitive cardholder data.
Government & e-services portals
Security assessment of citizen-facing government portals, e-services platforms, and public-sector web applications — aligned to Qatar's QNCSF and ictQATAR security directives.
Healthcare & patient portals
VAPT of hospital management systems, patient portals, and healthcare APIs — protecting sensitive patient data and ensuring compliance with Qatar Data Protection Law.
Retail & e-commerce platforms
Web application and API security testing for online retail platforms, shopping applications, and checkout flows — ensuring PCI-DSS compliance and protecting customer payment data.
SaaS & technology companies
Pre-launch and ongoing security testing for SaaS platforms, web applications, and APIs — helping technology companies demonstrate security assurance to enterprise clients and investors.
Energy & critical infrastructure
Assessment of operational technology web interfaces, vendor portals, and management platforms used by Qatar's energy and infrastructure sector — protecting critical national assets.
What clients say about our Managed IT Services


FAQ
What is a web application security assessment (VAPT)?
A web application VAPT (Vulnerability Assessment and Penetration Testing) is a structured security evaluation of your web application — combining automated scanning to identify known vulnerabilities with expert-led manual penetration testing to uncover complex issues that automated tools miss. The goal is to find security weaknesses in your application before attackers do, and provide you with a clear, prioritised plan to fix them. VAPT differs from a basic vulnerability scan in that it includes active exploitation attempts to validate the real-world impact of each finding.
What is the difference between a vulnerability assessment and a penetration test?
A vulnerability assessment identifies and catalogues security weaknesses in your application — it finds and lists the problems. A penetration test goes further — it actively attempts to exploit identified vulnerabilities to determine whether they can be used by a real attacker to gain unauthorised access or cause damage. Most organisations benefit from both combined as a VAPT engagement: the vulnerability assessment provides breadth, while penetration testing provides depth and validated proof of real-world impact. We always recommend combining both for comprehensive coverage.
What is the difference between black-box, grey-box, and white-box testing?
Black-box testing simulates an external attacker with no prior knowledge of the application — the tester starts from zero, as a real attacker would. Grey-box testing provides the tester with partial information — such as login credentials and basic architectural details — simulating an authenticated user or a partially informed attacker. White-box testing provides full access to source code, architecture documentation, and credentials — enabling the most thorough assessment. We recommend grey-box as the standard approach for most engagements, as it balances realism with coverage efficiency and is the most cost-effective use of testing time.
How often should we conduct a web application VAPT?
We recommend a minimum of once per year for most organisations, and more frequently — quarterly or with every major release — for high-risk applications such as financial platforms, payment systems, and healthcare portals. PCI-DSS mandates annual penetration testing and testing after significant changes. Beyond compliance, web applications change continuously — new features, updated dependencies, and configuration changes all introduce new vulnerabilities. A point-in-time annual test is a minimum; continuous or release-driven testing is best practice.
Will testing disrupt or damage our live application?
We take every precaution to minimise disruption to your live application. Before testing begins, we agree a testing schedule, out-of-hours testing windows if required, and a list of sensitive functionality to avoid (such as irreversible transactions or bulk email triggers). Our testers are experienced in performing controlled, professional assessments on production environments — but for highly sensitive systems, we recommend testing against a staging environment that mirrors production. We maintain an emergency contact protocol and can pause or stop testing immediately if any issue arises.
What does the OWASP Top 10 cover and why does it matter?
The OWASP (Open Web Application Security Project) Top 10 is the globally recognised standard list of the most critical web application security risks — updated regularly based on real-world attack data. It covers categories including broken access control, injection attacks, cryptographic failures, insecure design, and server-side request forgery. It matters because it is referenced by PCI-DSS, ISO 27001, QCB IT Risk Framework, and most security compliance standards as the minimum baseline for web application security testing. Every one of our VAPT assessments covers the full OWASP Top 10 as a guaranteed minimum — and goes further with business logic, API, and application-specific testing.
Do you test APIs as part of the web application assessment?
Yes — and this is a critical part of any modern web application assessment. We test REST and GraphQL APIs as a core component of our VAPT, covering the OWASP API Security Top 10 including broken object-level authorisation (BOLA), broken function-level authorisation (BFLA), excessive data exposure, mass assignment, lack of resource and rate limiting, and injection vulnerabilities in API endpoints. If your application has a separate mobile API or third-party integration layer, we can scope these for inclusion. Many significant breaches in Qatar and globally have resulted from inadequately secured APIs — this is not an optional extra.
How long does a web application VAPT take?
Duration depends on the size and complexity of the application. A small web application (10–20 pages, basic authentication) typically takes 3–5 days of testing. A medium-complexity application with authenticated areas, APIs, and multiple user roles typically takes 5–10 days. A large enterprise application with complex business logic, extensive API coverage, and multiple environments may take 2–4 weeks. We provide a detailed timeline estimate during scoping, including testing days, analysis time, and report delivery date — so you can plan your remediation timeline in advance.
