forensic investigations completed
average evidence acquisition turnaround
chain-of-custody compliance on all cases
years of forensic investigation experience
Why digital forensics & investigation matters
In the aftermath of a cyber incident, employee misconduct, fraud, or legal dispute — how digital evidence is collected, preserved, and analysed determines whether justice is served or cases are lost. Mishandled evidence is inadmissible evidence.
Evidence integrity is everything
Digital evidence that isn't properly acquired with write-blocking, hashed, and documented in a chain-of-custody log is routinely challenged — and rejected — in legal proceedings. First response matters.
Cyber incidents require forensic analysis
Understanding how attackers entered your systems, what they accessed, and how long they were present requires deep forensic analysis — not just incident containment. Without it, the same attack can happen again.
Insider threats are rising
Disgruntled employees, departing staff, and malicious insiders account for a significant and growing proportion of data theft, IP theft, and sabotage incidents — requiring forensic investigation to identify scope and perpetrators.
Legal & regulatory obligation
GDPR, FCA, and sector-specific regulations may require organisations to investigate and report breaches. A professional forensic report demonstrates compliance diligence and can limit regulatory liability.
Our digital forensics services
From reactive incident response to proactive e-discovery support — our forensic services cover the full spectrum of digital investigation needs across corporate, legal, and public sector environments.
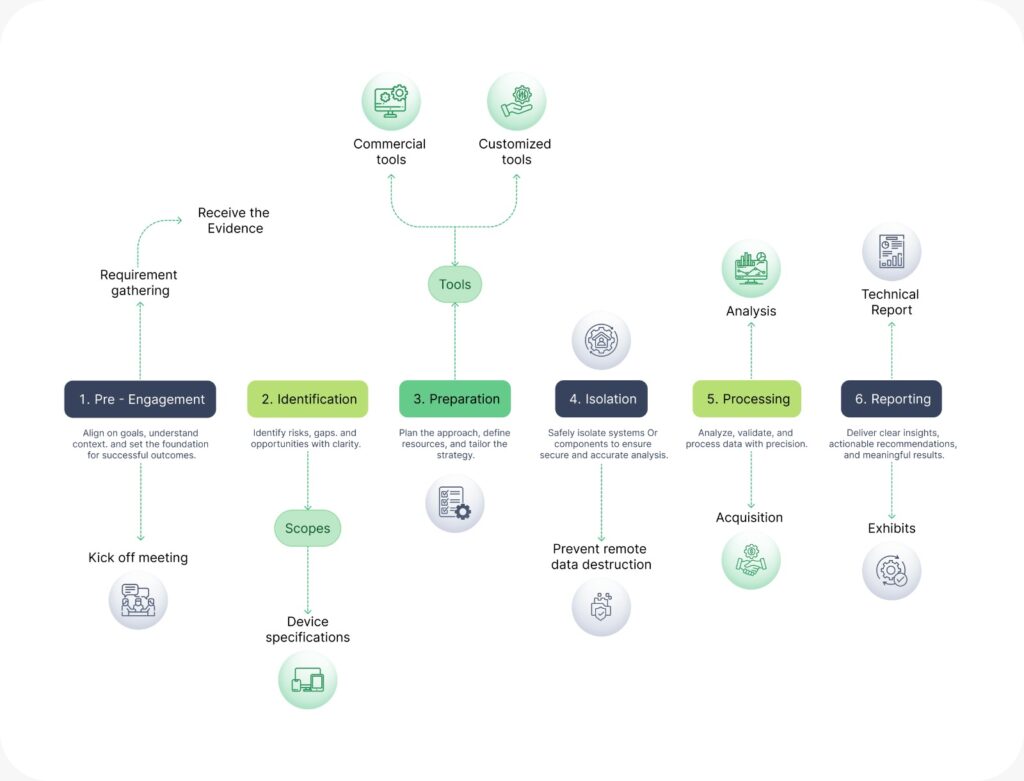
Our investigation process
Our forensic investigation process
Initial engagement & scoping
We begin with a confidential consultation to understand the nature of the incident or investigation, define the scope of evidence required, and establish the legal context — civil, criminal, regulatory, or internal HR. Rules of engagement and evidence objectives are agreed before any action is taken.
Forensic examination & data collection
Working on forensic copies — never originals — our investigators examine file systems, registry entries, browser artefacts, communication logs, application data, and system metadata. Deleted, hidden, and encrypted data is recovered using specialist forensic tooling.
Evidence preservation & acquisition
All digital evidence is acquired using industry-standard write-blocking techniques and forensic imaging tools. Every piece of evidence is cryptographically hashed (MD5/SHA-256) at acquisition and recorded in a formal chain-of-custody log — ensuring integrity and admissibility from the very first step.
Analysis & timeline reconstruction
Recovered data is correlated, cross-referenced, and assembled into a clear factual timeline of events. We identify who did what, when, from which device, and — where possible — establish intent. Our analysis is objective, fact-based, and documented to withstand legal scrutiny.
Learn More About Digital Forensics & Investigation
Watch our expert walkthrough and grab the detailed flyer to easily share with your team and stakeholders.
What you receive
Every forensic investigation includes a complete evidence and reporting package — designed for both technical and non-technical audiences, and ready for legal or regulatory use.
Executive investigation summary
Plain-English findings for senior leadership, legal counsel, and board-level stakeholders.
Detailed technical forensic report
Full methodology, tools used, findings, and technical analysis — reproducible and auditable.
Annotated evidence exhibits
Clearly labelled screenshots, file listings, communication extracts, and log excerpts supporting each finding.
Chain-of-custody documentation
Complete audit trail from evidence acquisition through to delivery — with hash values at every stage.
Event timeline & activity chronology
Visual and written chronology of user and system activity — showing what happened, when, and from where.
Expert witness statement (if required)
Formal CPR Part 35 compliant expert witness report prepared for court or tribunal submission.
Who we help
Our forensic investigation services are trusted by a wide range of organisations — from FTSE-listed companies to law firms, regulators, and government agencies.
Businesses & enterprises
Investigating data breaches, insider threats, fraud, misconduct, and competitive intelligence theft. Supporting board-level incident response.
Law firms & solicitors
Providing court-admissible forensic reports and expert witness testimony in civil, criminal, and employment tribunal proceedings.
Public sector & regulators
Supporting regulatory investigations, compliance audits, and public body incident response with forensically sound processes.
Financial services & fintech
Investigating financial fraud, rogue trading, data manipulation, and insider dealing — with outputs aligned to FCA regulatory expectations.
HR & people teams
Objective digital evidence collection for disciplinary hearings, grievance investigations, and employment disputes — handled with discretion.
Insurance & loss adjusters
Forensic analysis to support cyber insurance claims — validating incident timelines, quantifying data loss, and confirming attack attribution.
What clients say about our Managed IT Services


FAQ
What is digital forensics and investigation?
Digital forensics is the science of identifying, preserving, analysing, and presenting digital evidence from computers, mobile devices, networks, and cloud platforms. It is used in legal proceedings, HR investigations, regulatory compliance, and cyber incident response. The goal is always to recover accurate, admissible evidence while maintaining strict chain-of-custody integrity — so findings can be relied upon in court, tribunal, or internal proceedings.
What types of devices and systems can you investigate?
We investigate a wide range of digital sources including: computers (Windows, macOS, Linux), mobile devices (iOS and Android smartphones and tablets), cloud platforms (Microsoft 365, Google Workspace, AWS, Azure), email systems (Exchange, Outlook, Gmail), servers and network infrastructure, USB drives and external storage, CCTV and IoT devices, and messaging applications (WhatsApp, Telegram, Teams). If data exists digitally, we can investigate it.
How is digital forensics different from a standard IT investigation?
Standard IT troubleshooting is not forensically sound — it often modifies or destroys the very evidence you need. Digital forensics uses write-blocking hardware, forensic imaging tools, and cryptographic hashing to ensure evidence is acquired without alteration. Every action is documented in a formal chain-of-custody log. This evidential integrity is what makes forensic findings admissible in legal proceedings — something a standard IT investigation cannot provide.
How quickly can you respond to an urgent forensic investigation?
We offer 24/7 emergency response for urgent forensic matters. For critical incidents — active ransomware attacks, suspected ongoing data theft, or time-sensitive legal matters — our team can typically be deployed on-site in Qatar within a few hours of engagement. For non-urgent matters, we typically begin within one business day. Early engagement is always better — the sooner we are involved, the more evidence we can recover and preserve.
When should an organisation engage a digital forensics investigator?
You should engage a digital forensics investigator as soon as you suspect an incident — not after you have tried to investigate it yourself. Common triggers include: a suspected data breach or cyber attack, suspicion of employee misconduct or data theft, a fraud or financial irregularity, a legal dispute requiring digital evidence, or a regulatory investigation. Acting quickly is critical — digital evidence can be overwritten, corrupted, or lost within hours if not properly preserved.
Can you recover deleted files, messages, and emails?
In many cases, yes. When a file is deleted, the data is not immediately erased from storage — only the reference to it is removed. Using specialist forensic tools, we can often recover deleted files, emails, WhatsApp messages, browser history, and application data from computers, mobile devices, and cloud systems. The success of recovery depends on how long ago data was deleted, whether the storage has been overwritten, and the type of device. Acting quickly significantly increases recovery success rates.
What information do I need to provide at the start of an investigation?
To scope an investigation effectively, it helps to provide: a description of what happened or what you suspect, the types of devices or systems involved, the relevant timeframe, the legal or business context (e.g. HR dispute, cyber incident, fraud), and any applicable deadlines (court dates, regulatory reporting deadlines). You don’t need to have all the answers — our scoping consultation is designed to help you define the investigation objectives clearly before we begin.
How long does a digital forensics investigation take?
Timelines vary depending on the scope and complexity of the investigation. A focused single-device investigation (e.g., one laptop or mobile phone) typically takes 5–10 business days from evidence receipt to report delivery. A multi-device or enterprise-scale investigation involving cloud platforms, servers, and multiple devices may take 3–8 weeks. For urgent matters — active incidents, imminent legal deadlines — we offer expedited investigation services. We always provide a timeline estimate at the scoping stage before work begins.
