Clients Secured
Assessments Done
Vulnerabilities Found
Countries Served
Why Wireless Security Assessment Matters
Every organization faces these critical risks. Without proper assessment, these vulnerabilities become attack vectors for adversaries.
WPA2/WPA3 Authentication Attacks
PMKID capture, 4-way handshake cracking, Dragonblood attacks against WPA3, and enterprise RADIUS server vulnerabilities enabling unauthorized wireless access.
Evil Twin & Captive Portal Attacks
Spoofed SSIDs capturing credentials through fake login portals. We test whether your users and systems can distinguish legitimate APs from malicious ones.
Guest Network Breakout
Guest Wi-Fi with insufficient isolation from corporate networks. We test VLAN configuration, firewall rules, and routing to validate guest network segregation.
Rogue Access Point Detection
Unauthorized APs connected to your network - employee hotspots, implanted devices, and misconfigured equipment creating bypass paths around your security controls.
Client Isolation Failures
Wireless clients able to communicate directly - enabling lateral movement, credential harvesting, and device exploitation on the same wireless network.
Bluetooth & IoT Wireless Risks
BLE sniffing, Zigbee interception, and wireless peripheral exploitation. Non-Wi-Fi wireless protocols creating additional attack surfaces in your environment.
What We Assess
A comprehensive, methodical evaluation covering every critical surface area.
Learn More About cloud security assessment
Watch our expert walkthrough and grab the detailed flyer to easily share with your team and stakeholders.
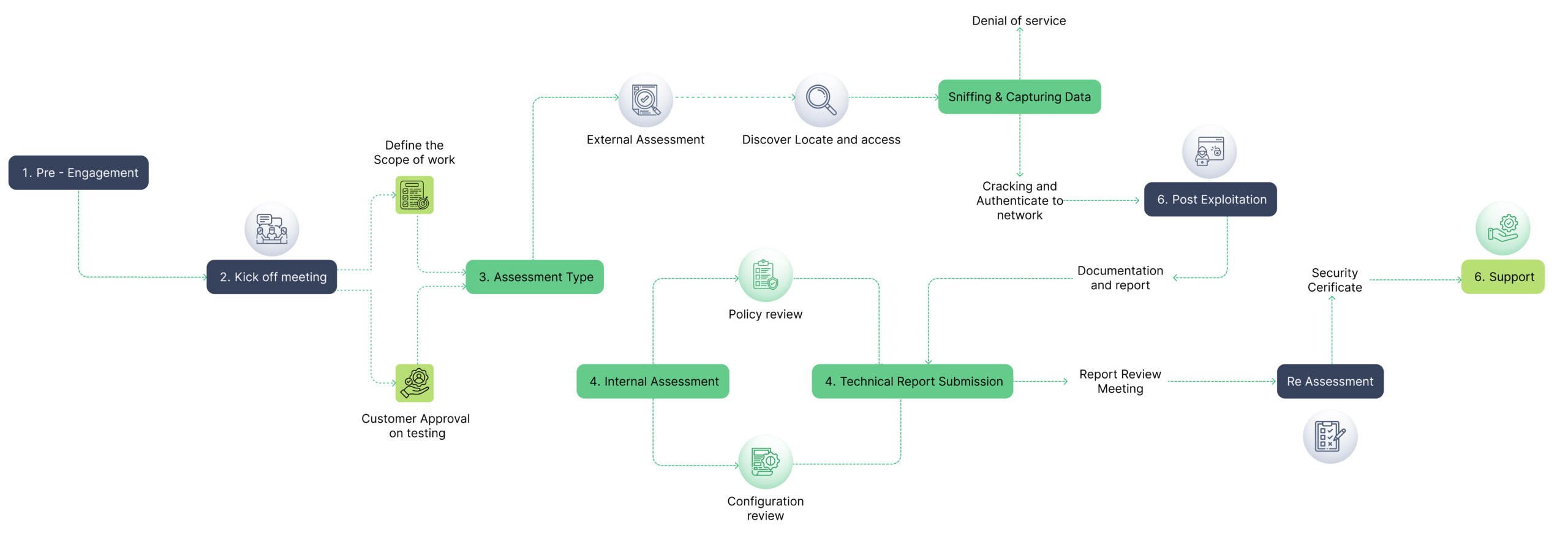
OUR METHODOLOGY
Assessment Process
A structured, repeatable methodology delivering consistent, high-quality results across every engagement.
Why Choose Us for Database Penetration Testing
We understand Purdue Model, IEC 62443, and the unique constraints of testing live industrial environments safely.
CREST
CREST-Approved for VA & PT
International gold standard in security testing – the only Indian company with dual CREST accreditation for both Vulnerability Assessment and Penetration Testing.
168K+
Vulnerabilities Discovered
Proven track record across 4,800+ assessments. Every finding is manually validated with proof-of-concept – zero false positives.
LURA
Real-Time Project Portal
Track assessment progress, view findings, and collaborate with our team through our proprietary LURA platform. Security Simplified.
What clients say about our Managed IT Services


Wireless Security Assessment FAQs
How long does the Wireless Security Assessment take?
Typically 1-3 weeks depending on scope and complexity. We provide a detailed timeline during the scoping phase based on your specific environment and requirements.
Will the assessment affect our production systems?
We use carefully controlled, non-destructive testing techniques for production environments. For invasive tests, we coordinate timing with your team and can test on staging environments.
What certifications do your testers hold?
Our team holds OSCP, CREST CRT, CEH, CISSP, and CISM certifications. Q-tech is CREST-approved for both Vulnerability Assessment and Penetration Testing – the only Indian company with this dual accreditation.
Do you provide re-testing after remediation?
Yes. We include one round of complimentary re-testing within 90 days to validate all findings have been properly remediated. The re-test report is provided through our LURA portal.
What deliverables do we receive?
You receive a comprehensive report with executive summary, detailed technical findings with CVSS scores, proof-of-concept demonstrations, risk-prioritized remediation guidance, and access to our LURA portal for ongoing tracking.
Get in Touch
Discuss Your OT Security Needs
Pick the channel that works best for you. We respond on all of them
Chat with our security team instantly
AI Chatbot
Ask our Al about OT/SCADA/ICS
Security
Secure Your Critical Infrastructure
Talk to our OT security specialists for a safe, thorough assessment of your industrial environment.
