Clients Secured
Assessments Done
Vulnerabilities Found
Countries Served
THREAT LANDSCAPE
Why Database Penetration Testing Matters
Every organization faces these critical risks. Without proper assessment, these vulnerabilities become attack vectors for adversaries.
SQL Injection & Query Manipulation
Advanced SQL injection testing including blind, time-based, out-of-band, and second-order injection attacks targeting database engines behind application layers.
Unencrypted Sensitive Data at Rest
PII, financial data, and credentials stored without encryption. We assess TDE configuration, column-level encryption, and backup encryption across all database platforms.
Stored Procedure & Trigger Vulnerabilities
Insecure stored procedures executing OS commands, dynamic SQL, and triggers that can be exploited for data exfiltration or privilege escalation.
Privilege Escalation in Databases
Testing for database-level privilege escalation - from read-only to DBA, exploiting misconfigurations in roles, grants, and stored procedures.
Default & Weak Database Credentials
Default SA/root passwords, weak authentication policies, and missing password rotation on database accounts - the most common entry point for database breaches.
Audit Trail & Logging Gaps
Missing or insufficient database audit logging - unable to detect unauthorized queries, data modifications, or privilege changes after a breach.
What We Assess
A comprehensive, methodical evaluation covering every critical surface area.
Learn More About cloud security assessment
Watch our expert walkthrough and grab the detailed flyer to easily share with your team and stakeholders.
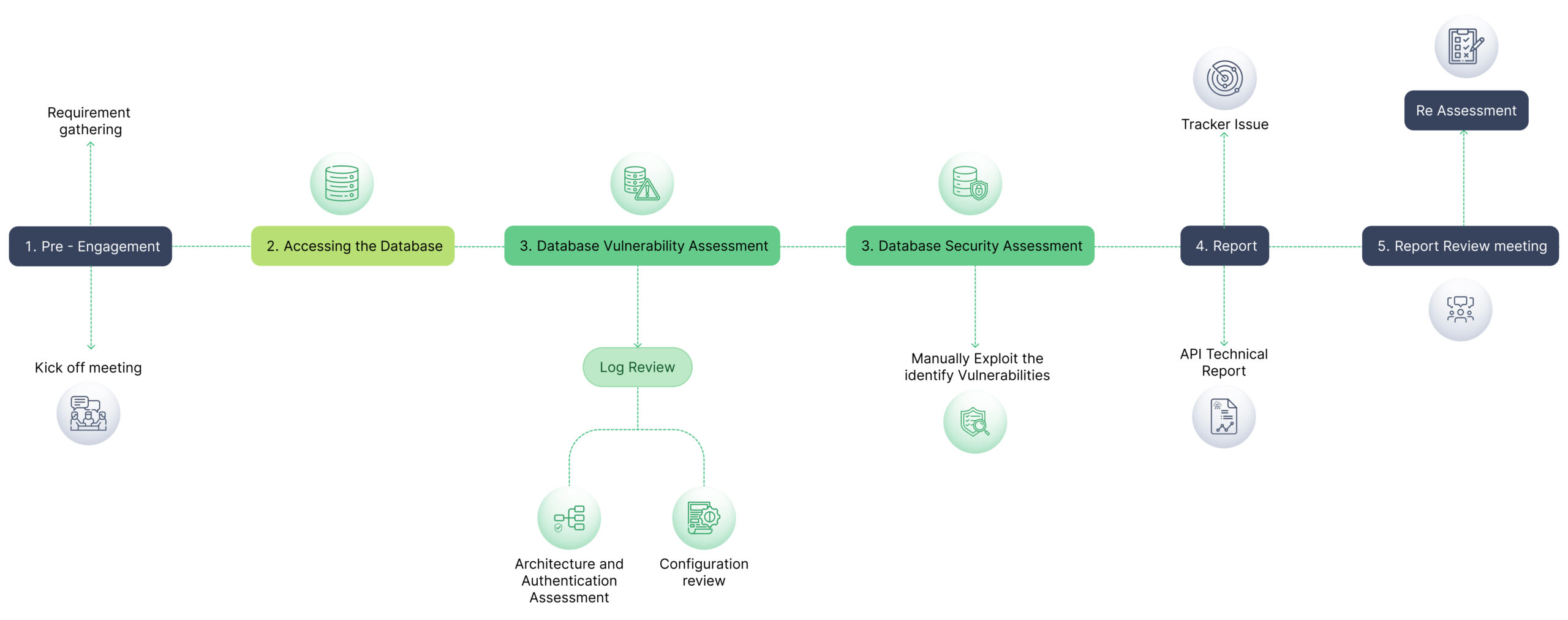
OUR METHODOLOGY
Assessment Process
A structured, repeatable methodology delivering consistent, high-quality results across every engagement.
Why Choose Us for Database Penetration Testing
We understand Purdue Model, IEC 62443, and the unique constraints of testing live industrial environments safely.
CREST
India’s Only CREST-Approved for VA & PT
International gold standard in security testing – the only Indian company with dual CREST accreditation for both Vulnerability Assessment and Penetration Testing.
168K+
Vulnerabilities Discovered
Proven track record across 4,800+ assessments. Every finding is manually validated with proof-of-concept – zero false positives.
LURA
Real-Time Project Portal
Track assessment progress, view findings, and collaborate with our team through our proprietary LURA platform. Security Simplified.
What clients say about our Managed IT Services


Database Penetration Testing FAQs
How long does the Database Penetration Testing take?
Typically 1-3 weeks depending on scope and complexity. We provide a detailed timeline during the scoping phase based on your specific environment and requirements.
Will the assessment affect our production systems?
We use carefully controlled, non-destructive testing techniques for production environments. For invasive tests, we coordinate timing with your team and can test on staging environments.
What certifications do your testers hold?
Our team holds OSCP, CREST CRT, CEH, CISSP, and CISM certifications. Briskinfosec is CREST-approved for both Vulnerability Assessment and Penetration Testing – the only Indian company with this dual accreditation.
Do you provide re-testing after remediation?
Yes. We include one round of complimentary re-testing within 90 days to validate all findings have been properly remediated. The re-test report is provided through our LURA portal.
What deliverables do we receive?
You receive a comprehensive report with executive summary, detailed technical findings with CVSS scores, proof-of-concept demonstrations, risk-prioritized remediation guidance, and access to our LURA portal for ongoing tracking.
Get in Touch
Discuss Your OT Security Needs
Pick the channel that works best for you. We respond on all of them
Chat with our security team instantly
AI Chatbot
Ask our Al about OT/SCADA/ICS
Security
Secure Your Critical Infrastructure
Talk to our OT security specialists for a safe, thorough assessment of your industrial environment.
