of web traffic is now API-based — making APIs the primary attack surface for modern applications
of mobile apps fail basic security tests on first assessment
mobile application assessments completed across Qatar & GCC
free remediation retest included on every mobile app engagement
Why API security testing matters
APIs are the invisible infrastructure powering every modern application — your mobile app, web platform, third-party integrations, and microservices all communicate through them. In Qatar’s rapidly digitising economy, they are the most frequently targeted and least thoroughly tested attack surface in organisations of every size.
APIs bypass your perimeter security entirely
Traditional firewalls and WAFs are designed to filter web traffic — not to understand API business logic. An attacker who discovers an unsecured API endpoint can bypass your entire perimeter, access backend data directly, and exfiltrate thousands of records without triggering a single network-level alert.
APIs expose far more data than the UI shows
Excessive data exposure is endemic in API design — APIs frequently return entire database objects including fields never displayed in the UI. Sensitive personal details, financial information, and access tokens are routinely leaked through API responses to anyone who inspects the traffic.
Broken authorisation exposes every user's data
BOLA — the number one OWASP API vulnerability — allows any authenticated user to access any other user's data simply by changing an ID in an API request. A single BOLA vulnerability in a Qatar banking or healthcare API can expose every customer record in the database.
API abuse drives Qatar's most significant data breaches
The majority of significant data breaches in Qatar's financial, healthcare, and government sectors involve API vulnerabilities — not network intrusions. Credential stuffing via auth APIs, mass data scraping through poorly rate-limited endpoints, and BOLA exploitation are the primary attack patterns observed across the GCC.
What our mobile app security assessment covers
Our assessment covers both iOS and Android platforms — combining static analysis, dynamic runtime testing, network traffic interception, and manual expert review aligned to the OWASP Mobile Application Security Verification Standard (MASVS).
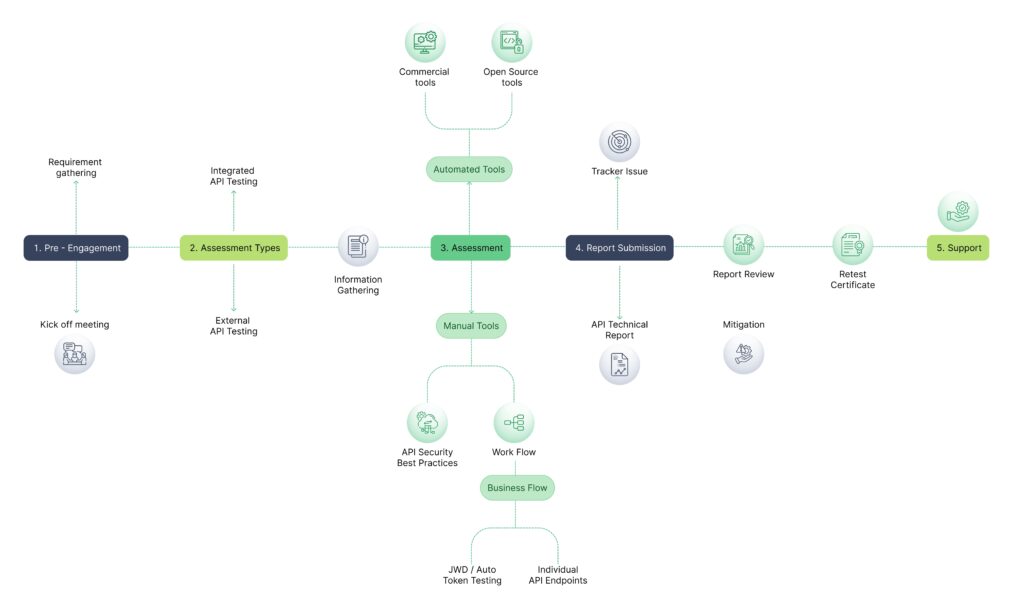
Our API security testing methodology
Our API security testing methodology
Scoping & API inventory
We begin with a detailed scoping session to define the API types in scope, testing environments, authentication mechanisms, and any sensitive endpoints requiring special handling. We also conduct an initial API discovery exercise — identifying undocumented and shadow API endpoints beyond those in the official specification.
Authentication & authorisation testing
We systematically test every authentication and authorisation mechanism — verifying tokens cannot be forged, that role-based access controls are enforced at the API layer, that horizontal and vertical privilege escalation are not possible, and that every authenticated endpoint correctly validates identity and permissions for each specific resource and action

Documentation & endpoint analysis
We analyse all available API documentation — OpenAPI/Swagger specs, Postman collections, WSDL files, GraphQL schemas — to map the full attack surface. Active endpoint discovery, parameter fuzzing, and traffic analysis identify endpoints not in official documentation. A comprehensive attack surface map is produced before exploitation testing begins.
Reporting & risk rating
You receive a dual-audience report — an executive summary for leadership with business risk context, and a detailed technical report for your development and API teams with endpoint-level findings, HTTP request/response captures, reproduction steps, and specific remediation guidance. Every finding is CVSS-scored and mapped to the OWASP API Security Top 10.
Learn More About API security testing
Watch our expert walkthrough and grab the detailed flyer to easily share with your team and stakeholders.
What you receive
Every API security assessment includes a complete testing and reporting package — structured for development teams, security leadership, compliance submissions, and client due diligence requirements.
Executive summary report
Plain-English risk overview for leadership — with business impact framing, data breach risk context, and overall API security posture rating.
Detailed technical findings report
Endpoint-level vulnerability descriptions, HTTP request/response captures, reproduction steps, proof-of-concept demonstrations, and remediation guidance for each finding.
CVSS-scored vulnerability register
Every finding rated Critical, High, Medium, Low, and Informational — with CVSS v3.1 scores and OWASP API Security Top 10 category mapping.
Complete API endpoint inventory
A full map of all tested endpoints including shadow and undocumented APIs discovered — your definitive API attack surface register.
Compliance mapping
Findings mapped to OWASP API Security Top 10, PCI-DSS, ISO 27001, Qatar Data Protection Law, and QCB IT Risk Framework requirements.
Prioritised remediation roadmap
Sprint-ready fix plan prioritised by business impact — structured for integration into your API development workflow with acceptance criteria per fix.
Who we help
Our API security testing serves organisations across Qatar and the GCC — from financial institutions with complex microservice architectures to startups launching their first public API and government entities digitalising citizen services.
Open banking & payment APIs
API security testing for open banking platforms, payment processing APIs, and QCB-mandated open API implementations — protecting financial data and ensuring PCI-DSS and QCB IT Risk Framework compliance.
Government & e-services APIs
Security assessment of APIs underpinning Qatar's digital government services — citizen data APIs, inter-agency integration layers aligned to QNCSF and ictQATAR security requirements.
Healthcare & patient data APIs
API testing for hospital information systems, FHIR-based health data APIs, and laboratory integration services — ensuring patient data protection and Qatar Data Protection Law compliance.
SaaS platforms & developer APIs
Public and private API security testing for SaaS platforms and microservice architectures — providing security assurance for enterprise clients and embedding security into the API development lifecycle.
E-commerce & payment APIs
Security assessment of product catalogue APIs, order management endpoints, loyalty platform integrations, and payment gateway APIs — protecting customer data and ensuring PCI-DSS compliance.
OT/IT integration & industrial APIs
Security testing of APIs bridging operational technology and IT systems — vendor portal APIs, SCADA integration endpoints, and industrial IoT APIs used by Qatar's energy and critical infrastructure sectors.
What clients say about our Managed IT Services


FAQ
What is API security testing?
API security testing is a structured assessment of the security of your application programming interfaces — the endpoints through which your web application, mobile app, third-party integrations, and microservices communicate. It combines automated scanning with expert manual testing to identify vulnerabilities including broken authorisation, authentication weaknesses, data over-exposure, injection flaws, rate limiting bypass, and business logic abuse. Unlike a web application VAPT that tests the UI layer, API security testing focuses specifically on the underlying API layer — often revealing vulnerabilities completely invisible when testing through the application interface alone.
What is the OWASP API Security Top 10 and why does it matter?
The OWASP API Security Top 10 is the globally recognised list of the most critical API security risks — published by the Open Web Application Security Project and updated based on real-world breach data. It covers categories from Broken Object Level Authorisation (API1) and Broken Authentication (API2) through to Unsafe API Consumption (API10). It matters because it is referenced by PCI-DSS, ISO 27001, QCB IT Risk Framework, and Qatar’s broader regulatory guidance as the standard framework for API security testing. Every one of our API assessments guarantees full coverage of the OWASP API Security Top 10 as a minimum baseline — we then extend beyond it with business logic testing, JWT analysis, and protocol-specific testing.
How is API security testing different from a web application VAPT?
A web application VAPT tests security through the browser interface — clicking forms, testing input fields, and analysing what the UI renders. API security testing bypasses the UI entirely and tests the underlying data layer directly — manipulating API requests, testing authorisation at the endpoint level, fuzzing parameters the UI never exposes, and testing inter-service communication with no UI at all. Many organisations conduct web application VAPT and believe their APIs are covered — they are not. The most critical API vulnerabilities, including BOLA and BFLA, require direct API-layer testing that web application methodologies are not designed to find. We recommend both as complementary assessments for any application with a significant API attack surface.
What API types do you test — REST, GraphQL, SOAP, gRPC?
Yes — we test all major API protocols. REST APIs are our highest-volume assessment type. GraphQL APIs require specialist testing tools and methodology due to their flexible query structure and unique vulnerability patterns. SOAP and XML-based APIs are common in Qatar’s banking and government sectors and require specific XML injection and XXE testing. gRPC APIs using Protobuf over HTTP/2 are an emerging testing area for cloud-native microservice architectures. We also test WebSocket APIs, OAuth 2.0 / OpenID Connect flows, and event-driven messaging APIs. We assess each protocol using the appropriate specialist tooling and methodology for its specific vulnerability patterns.
How often should we conduct an API security assessment?
We recommend a minimum of once per year for most organisations, and more frequently for APIs that change regularly or handle high-value data. API testing should also be triggered by major new API features or endpoint additions, significant changes to authentication or authorisation logic, onboarding of new third-party API integrations, before a public API launch, and when required for compliance. For organisations with continuous deployment, embedding API security testing into CI/CD pipelines provides the most comprehensive ongoing protection — we can advise on tooling and process for DevSecOps API security integration.
What is BOLA (Broken Object Level Authorisation) and why is it so dangerous?
BOLA — also known as IDOR — is the number one vulnerability in the OWASP API Security Top 10. It occurs when an API endpoint accepts a resource identifier in a request but fails to verify whether the requesting user is actually authorised to access that specific resource. An attacker simply changes the ID in the request — for example, changing /api/accounts/1001 to /api/accounts/1002 — and receives another user’s account data. In a banking or healthcare API, a single BOLA vulnerability can expose every customer record in the database. It is dangerous because it is both extremely common and requires zero technical sophistication to exploit once discovered.
Do you test the APIs behind our mobile app as well as our web application?
Yes — and this is one of the most valuable testing scenarios. Mobile apps and web applications often share the same backend API, but the mobile API layer is frequently less well-tested and may have additional endpoints not exposed through the web interface. We can conduct a combined assessment that covers the backend API from multiple access perspectives — web client, mobile client, and direct API access — ensuring endpoint-level vulnerabilities are identified regardless of which interface an attacker uses. A combined assessment also identifies API endpoints accessible via mobile but not web (or vice versa) that might be overlooked in single-surface testing.
Can you discover API endpoints we don't know about?
Yes — shadow API and endpoint discovery is a standard component of every assessment. We use a combination of techniques: analysis of JavaScript bundles and mobile app binaries for hardcoded API paths; directory and endpoint fuzzing using framework-specific wordlists; traffic analysis during application use to capture all API calls; examination of error messages and verbose responses that reveal internal endpoint structures; and review of any available CI/CD artifacts or developer documentation. Most organisations are surprised by how many active API endpoints exist beyond their official documentation — these undocumented endpoints are the highest-risk category because they are never monitored and never tested.
