Clients Secured
Assessments Done
Vulnerabilities Found
Countries Served
Why Secure Code Review Matters
Every organization faces these critical risks. Without proper assessment, these vulnerabilities become attack vectors for adversaries.
Injection Vulnerabilities in Source Code
Employee credentials, customer databases, and corporate secrets traded on dark web forums. We monitor 15,000+ sources for your organization’s leaked data in real-time.
Insecure Cryptographic Implementation
Weak algorithms (MD5, SHA1, DES), predictable random number generators, improper key management, and custom crypto implementations that undermine data protection.
Insecure Third-Party Dependencies
Vulnerable libraries, outdated frameworks, and transitive dependency risks. We analyze your SBOM for known CVEs and license compliance issues.
Hardcoded Credentials & API Keys
Secrets committed to repositories – database passwords, API tokens, encryption keys, and cloud credentials that attackers harvest from source code and commit history.
Race Conditions & Concurrency Issues
Time-of-check-to-time-of-use (TOCTOU) vulnerabilities, deadlocks, and thread-safety issues that create exploitable windows in multi-threaded applications.
Business Logic Errors in Code
Flawed validation, missing authorization checks, integer overflow, and logic bypass conditions that automated scanners miss but manual review catches.
What We Assess
A comprehensive, methodical evaluation covering every critical surface area.
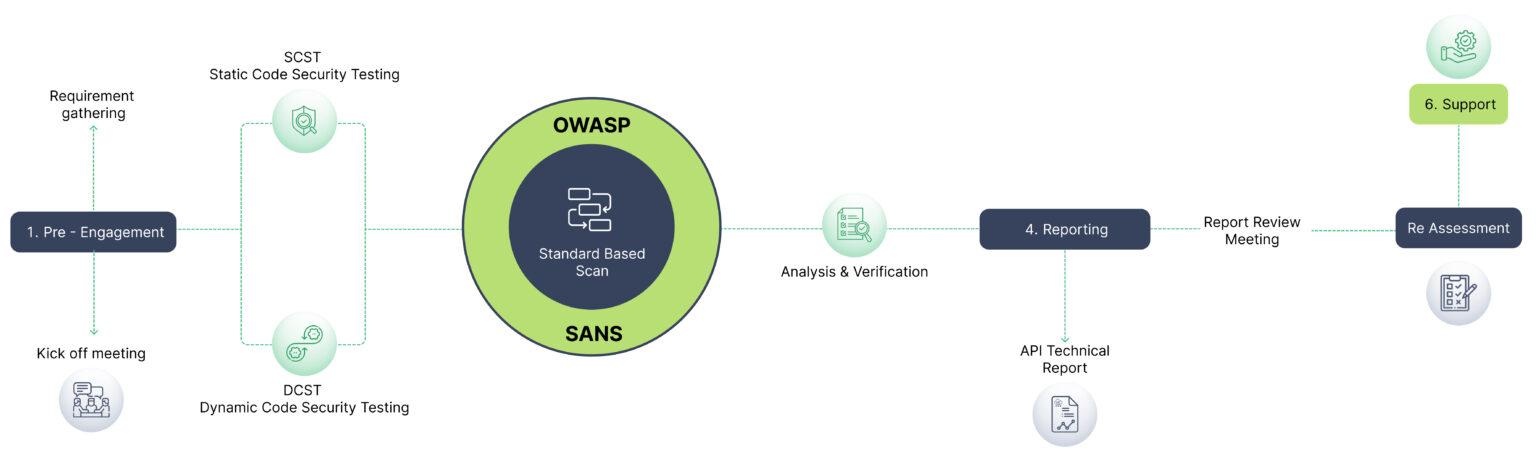
Assessment Process
A structured, repeatable methodology delivering consistent, high-quality results across every engagement.
Learn More About Secure Code Review
Watch our expert walkthrough and grab the detailed flyer to easily share with your team and stakeholders.
Why Choose Us for Secure Code Review
We understand Purdue Model, IEC 62443, and the unique constraints of testing live industrial environments safely.
CREST
CREST-Approved for VA & PT
International gold standard in security testing – the only Indian company with dual CREST accreditation for both Vulnerability Assessment and Penetration Testing.
168K+
Vulnerabilities Discovered
Proven track record across 4,800+ assessments. Every finding is manually validated with proof-of-concept – zero false positives.
LURA
Real-Time Project Portal
Track assessment progress, view findings, and collaborate with our team through our proprietary LURA platform. Security Simplified.
What clients say about our Managed IT Services


Secure Code Review FAQs
How long does the Secure Code Review take?
Typically 1-3 weeks depending on scope and complexity. We provide a detailed timeline during the scoping phase based on your specific environment and requirements.
Will the assessment affect our production systems?
We use carefully controlled, non-destructive testing techniques for production environments. For invasive tests, we coordinate timing with your team and can test on staging environments.
What certifications do your testers hold?
Our team holds OSCP, CREST CRT, CEH, CISSP, and CISM certifications. Q-tech is CREST-approved for both Vulnerability Assessment and Penetration Testing – the only Indian company with this dual accreditation.
Do you provide re-testing after remediation?
Yes. We include one round of complimentary re-testing within 90 days to validate all findings have been properly remediated. The re-test report is provided through our LURA portal.
What deliverables do we receive?
You receive a comprehensive report with executive summary, detailed technical findings with CVSS scores, proof-of-concept demonstrations, risk-prioritized remediation guidance, and access to our LURA portal for ongoing tracking.
Get in Touch
Discuss Your OT Security Needs
Pick the channel that works best for you. We respond on all of them
Chat with our security team instantly
AI Chatbot
Ask our Al about OT/SCADA/ICS
Security
Secure Your Critical Infrastructure
Talk to our OT security specialists for a safe, thorough assessment of your industrial environment.
